YouTube has issued a warning about scammers using an AI-generated video of CEO Neal Mohan in phishing attacks. These attacks involve private videos sent to targeted users, falsely announcing changes to YouTube's monetization policy. The emails prompt recipients to click a link, leading to a fake page where they are asked to confirm updated YouTube Partner Program (YPP) terms by signing into their account; however, this page is designed to steal their credentials.
Scammers create urgency by threatening account restrictions if users fail to comply. YouTube advises users not to click on links in private videos and to report suspicious emails. Many creators have fallen victim, with scammers hijacking channels to broadcast cryptocurrency scam streams. YouTube provides tips and a support assistant to help users recover hacked accounts.
Key takeaways:
AI-Generated Phishing: Scammers are using AI to impersonate YouTube's CEO.
Private Video Scam: YouTube will never share information via private videos.
Account Restriction Threats: Scammers threaten account restrictions to create urgency.
Credential Theft: The phishing page is designed to steal user credentials.
Recovery Assistance: YouTube offers tools to help users recover hacked accounts.

💻 Malware and Vulnerabilities
Ransomware gangs are exploiting a Paragon Partition Manager flaw using 'Bring Your Own Vulnerable Driver' (BYOVD) attacks. This allows threat actors to escalate privileges and bypass security. Microsoft discovered five flaws, with CVE-2025-0289 being actively exploited. Users should update to the latest version and enable the Microsoft Vulnerable Driver Blocklist. The blocklist prevents vulnerable drivers from being used.
Ransomware Boss's Courtroom Escape - Oleg Nefedov, an alleged leader of the Black Basta ransomware gang, was arrested in Armenia but escaped from custody with the help of high-level officials. After being detained, Nefedov was released during a court hearing and fled in a vehicle. Internal messages suggest he had "friends at a really high level" who facilitated his escape. Intel 471 notes the connections between Russian intelligence and cybercriminals. The leaked chats also revealed Nefedov's activities, including property purchases in Dubai.
Critical Flaw in Chaty Pro WordPress Plugin - A critical vulnerability, CVE-2025-26776 (CVSS 10), in the Chaty Pro plugin for WordPress, could allow attackers to take over websites. The plugin, used by approximately 18,000 sites, has an arbitrary file upload vulnerability due to a lack of authorization and security checks. An attacker can upload a malicious file and compromise the WordPress site. Although a whitelist of allowed file extensions exists, it was not implemented. Users are strongly advised to update to version 3.3.4 or later, which includes a patch using the secure wp_handle_upload() function and proper file checks.
PayPal Phishing Scam Exploits Docusign API Scammers are abusing the Docusign API to send phishing emails impersonating PayPal. By using Docusign's API, phishers send legitimate-looking invoices, bypassing security filters. These emails often mention unauthorized transactions and urge immediate contact. To verify, check Docusign directly for the document using the security code in the email.
📈 Breaches and Incidents
ECB Payment System Meltdown - A hardware failure caused a 10-hour crash in the European Central Bank's payment system, delaying salaries and welfare for thousands. The Target 2 and Target 2 Securities (T2S) networks went down, requiring emergency channels for critical payments. The ECB is analyzing why backups failed to activate. The incident raised questions about the resilience of critical financial infrastructure.
Tata Technologies Hit by Ransomware - Hunters International claims responsibility for a ransomware attack on Tata Technologies, saying they stole 1.4TB of data (730,000 files). While Tata reported minimal impact from the January 2025 breach, the attackers threaten to release data if demands aren't met. Hunters International, possibly a rebrand of Hive, is known for aggressive tactics, targeting various sectors.
Microsoft 365 Outage Linked to Buggy Update - A coding issue in a recent Microsoft 365 update caused a widespread outage affecting Outlook, Exchange Online, Teams, and Power Platform. The outage, which started and ended within an hour, also led to Purview access issues. Microsoft resolved the problem by reverting the buggy code change and is reviewing its change management process. While the main issues are resolved, some Exchange Online users on iOS may still face problems.
Cyberattack on Polish Space Agency (POLSA) experienced unauthorized access to its IT infrastructure. Polish cybersecurity services secured the systems under attack and are investigating the incident. The POLSA network was disconnected from the Internet to secure data. This comes amid Polish accusations against Moscow for attempts to destabilize Poland. Poland's Prime Minister also accused Russia of planning acts of air terror against airlines worldwide.
UK National Health Service is investigating a data leak at Medefer, a healthcare partner, where patient data may have been exposed for up to six years. An IT whistleblower reported the unsecured API. The company CEO said the vulnerability was patched, but the exposure duration is unknown. Exposed data includes names, addresses, NHS numbers, and some doctor's notes.
Cyberattack Disrupts Russian Telecom Beeline Russian telecom Beeline faced a DDoS attack disrupting internet access and mobile app services for its 44 million subscribers. This follows a similar attack on Beeline in February and another on MegaFon in January. Experts suggest these are significant hacktivist attacks, with the attack on MegaFon originating from 3,300 IP addresses and Beeline from 1,600.
🚨 Threat Intel & Info Sharing
DOJ has charged 12 Chinese hackers linked to the government, accusing them of hacking over 100 American organizations, including the U.S. Treasury. The hackers, including members of APT27 (Silk Typhoon), targeted organizations to suppress free speech and religious freedoms, and stole data to sell to third parties. Victims spanned tech companies, think tanks, and healthcare systems. Some hackers worked for I-Soon, generating millions via widespread campaigns. Rewards are offered for information leading to their capture.
ATM Jackpotting Nets Two Venezuelans Two Venezuelan nationals David Jose Gomez-Cegarra, 24, and Jesus Segundo Hernandez-Gil, 19, were arrested in the U.S. for ATM jackpotting. They allegedly stole over $110,000 from a New York ATM after installing malware using a key to remove the ATM's cover. Investigators link them to additional attacks in New York, Massachusetts, and Illinois, totaling $187,000 in losses. They face up to 10 years in prison on charges of bank theft and conspiracy.
Cyber-Espionage Campaign Targets UAE A new cyber-espionage campaign, attributed to UNK_CraftyCamel, targeted aviation, satellite communications, and transportation infrastructure in the UAE. The attackers used malicious emails with polyglot files to deploy a new backdoor named Sosano. Sosano, written in Golang, connects to a command-and-control server to await commands. Security teams can monitor for LNK files, URL files, and executables accessing JPG files to detect the malware. Organizations should train users to be cautious of unexpected content.
⚖️ Laws, Policies and Regulations
CISA's Russia Cyber Stance - Despite a policy shift to pause offensive cyber ops during negotiations, CISA maintains its defense against Russian cyber threats to U.S. critical infrastructure. CISA denies any change in its posture, labeling reports to the contrary as "fake". The agency is undergoing a leadership transition.
Bybit's Stolen Funds "Gone Dark" Following a sophisticated cyberattack, Bybit CEO Ben Zhou reports that nearly 20% of the $1.46 billion stolen in crypto funds has become untraceable due to mixing services. While 77% remains traceable, approximately $1 billion was converted into Bitcoin. The exchange is working to freeze funds and has paid out over $2.1 million in bounty rewards. THORChain was heavily used in the laundering process.
UK Investigates Social Media Child Data - The ICO is investigating how TikTok, Reddit, and Imgur protect children's privacy in the UK. TikTok's use of data from 13–17-year-olds for recommendations is under scrutiny. Reddit and Imgur are being investigated for their age verification measures. The aim is to ensure these platforms comply with data protection laws and the Children’s code. The ICO has already driven privacy changes on other platforms.
France Boosts Intelligence Access - France is set to enhance its intelligence capabilities by requiring platforms to implement technical measures that allow intelligence services access to intelligible content and data. This access is limited to data with specific authorization. Non-compliance could result in penalties up to 2% of global annual turnover for corporations. The goal is to counter encrypted messaging used by criminals and terrorists.
Darknet Marketplace Sanctioned - The U.S. Treasury sanctioned Behrouz Parsarad, administrator of the darknet marketplace Nemesis, which facilitated nearly $30 million in drug sales. Nemesis was taken down in 2024, but Parsarad seeks to create a new marketplace. The U.S. is committed to dismantling these marketplaces.
ECB Outsourcing Trends in the Financial Sector - The ECB's 2024 Outsourcing Register reveals key trends in the financial sector, including a rise in active outsourcing contracts. SIs rely heavily on ICT services and cloud outsourcing. Sub-outsourcing is common, often to external providers. There's increased dependence on external providers, particularly in the US, and on services performed outside the EU. A large portion of the budget is concentrated among the top providers.
ECB's IT Risk Questionnaire Published - The ECB released its 2024 IT Risk Questionnaire (ITRQ) for transparency, covering January to December 2023. This standardized data collection tool, aligned with EBA guidelines, assesses IT risks in supervised credit institutions. The ITRQ includes thematic reviews and cyber incident reporting. Supervised entities must complete the questionnaire by February 29, 2024. The ITRQ addresses various aspects such as IT staff, expenses, outsourcing, and security. It also covers IT governance, risk management, and operational resilience.
NIS2 Compliance Challenges for Critical Sectors The EU's security agency, ENISA, reports that six critical infrastructure sectors are struggling to comply with the NIS2 directive. These sectors include IT service management, space, public administrations, maritime, health, and gas. Digital infrastructure also lags in maturity. Electricity, telecoms, and banking are more mature, benefiting from regulatory oversight and investment. A lack of skilled IT/OT security professionals hampers compliance. Organizations should secure data moving in and out of OT networks.
⚖️ Cybersecurity Start Ups and VCs
SpecterOps Raises $75M for Identity Security a cybersecurity startup, raised $75M in Series B funding to scale its BloodHound Enterprise platform, which detects and removes identity-based attack paths. Their platform maps and quantifies identity attack paths across IT infrastructures. SpecterOps also developed the open-source BloodHound Community Edition, which maps Active Directory attack paths. Cisco Investments participated in the funding round, supporting SpecterOps' approach to identity security. The funding will also support research, consulting, sales, and marketing efforts.
📊 Trends, Reports, Analysis
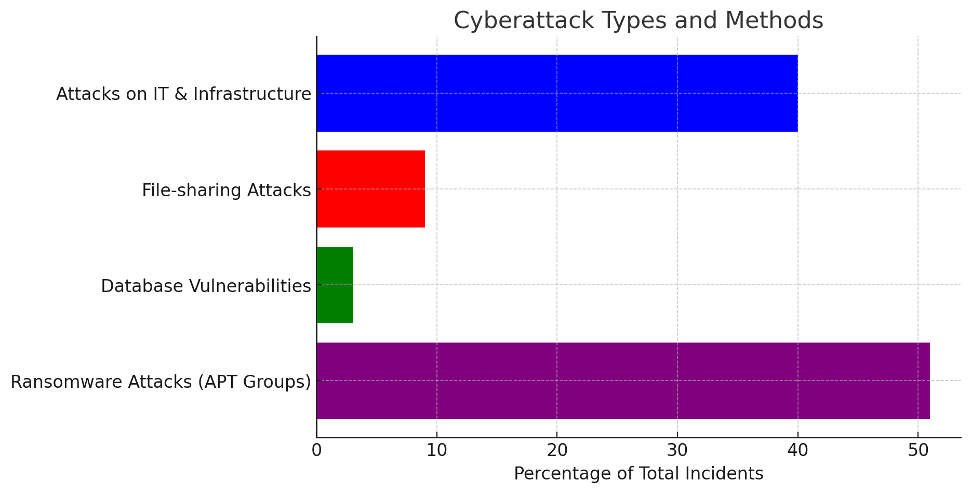
UAE Battles 200K Daily Cyberattacks - The UAE Cyber Security Council (CSC) thwarts over 200,000 cyberattacks daily from 14 countries, targeting strategic sectors. Government faces 30% of attacks, followed by finance/banking and education at 7% each. Common methods include DoS attacks, encryption/data leakage, and ransomware. AI-enhanced malware and deepfakes pose growing threats. The UAE urges strong security protocols and awareness.

DPRK IT Workers Posing as Foreign Nationals
A network of likely North Korean (DPRK)-affiliated IT workers are posing as Vietnamese, Japanese, and Singaporean nationals to obtain remote engineering and blockchain developer jobs. These personas target companies globally, including in Japan and the United States. They often lack social media but have profiles on job sites. Digitally manipulated photos and shared contact info link them. The goal: earn cash for Pyongyang’s weapons programs.
📅 Upcoming Events
🚀 Join us for an exclusive virtual event in March, where AI and cybersecurity experts will discuss how AI and Machine Learning are revolutionizing cyber defense. This session will feature expert panel discussions exploring AI-driven threat detection, automated response strategies, and the future of intelligent security.
This is a limited virtual event tailored for CISOs and executives. It is free to join so register today Form

We hope you enjoyed our email briefing! ☕🥮If you want to sponsor our next edition or advertise on our site, drop us an email [email protected].
Thank you for being a part of our newsletter community and you can be part of the community by joining our LinkedIn Group.

